Kubernetes (k8s) 集群部署(三) 完整版
第三步 Master节点部署
Master 是 Kubernetes 的大总管,主要创建apiserver、Controller manager与Scheduler来组件管理所有 Node。本步骤将下载 Kubernetes 并安装至 master1上,然后产生相关 TLS Cert 与 CA 密钥,提供给集群组件认证使用。
下载 Kubernetes 组件
1.下载所有需要的执行文件并解压:
$ cd && wget https://dl.k8s.io/v1.10.1/kubernetes.tar.gz
$ wget https://dl.k8s.io/v1.10.1/kubernetes-server-linux-amd64.tar.gz
$ wget https://dl.k8s.io/v1.10.1/kubernetes-client-linux-amd64.tar.gz
$ wget https://dl.k8s.io/v1.10.1/kubernetes-node-linux-amd64.tar.gz
$ tar -zxvf kubernetes.tar.gz
$ tar -zxvf kubernetes-server-linux-amd64.tar.gz
$ tar -zxvf kubernetes-client-linux-amd64.tar.gz
$ tar -zxvf kubernetes-node-linux-amd64.tar.gz
$ cp kubernetes/server/bin/kube-apiserver /usr/local/bin/
$ cp kubernetes/server/bin/kube-controller-manager /usr/local/bin/
$ cp kubernetes/server/bin/kube-scheduler /usr/local/bin/
$ mkdir -p /usr/local/bin/cni/ && cd /usr/local/bin/cni/
$ wget https://github.com/containernetworking/plugins/releases/download/v0.6.0/cni-plugins-amd64-v0.6.0.tgz
$ tar -zxvf cni-plugins-amd64-v0.6.0.tgz && rm -rf cni-plugins-amd64-v0.6.0.tgz2.创建集群 CA 与 Certificates
在这部分,将会需要生成 client 与 server 的各组件 certificates,并且替 Kubernetes admin user 生成 client 证书。
- 创建生成CSR的 JSON 配置文件:
$ cd /etc/etcd/ssl_tmp/
$ cat > /etc/etcd/ssl_tmp/kubernetes-csr.json <<EOF
{
"CN": "kubernetes",
"hosts": [
"127.0.0.1",
"192.168.184.28",
"10.1.0.1",
"10.254.0.2",
"kubernetes",
"kubernetes.default",
"kubernetes.default.svc",
"kubernetes.default.svc.cluster",
"kubernetes.default.svc.cluster.local"
],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"ST": "BeiJing",
"L": "BeiJing",
"O": "k8s",
"OU": "System"
}
]
}
EOF- 创建生成CSR的 JSON 配置文件:
$ cfssl gencert -ca=/etc/etcd/ssl/ca.pem -ca-key=/etc/etcd/ssl/ca-key.pem -config=/etc/etcd/ssl/ca-config.json -profile=kubernetes kubernetes-csr.json | cfssljson -bare kubernetes- 生成 kubernetes 证书和私钥,并分发到所以节点
$ cp kubernetes* /etc/etcd/ssl/
$ scp kubernetes* 192.168.184.29:/etc/etcd/ssl/
$ scp kubernetes* 192.168.184.30:/etc/etcd/ssl/- 创建 kube-apiserver 使用的客户端 token 文件
$ head -c 16 /dev/urandom | od -An -t x | tr -d ' '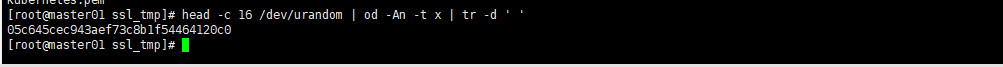
$ vim /etc/etcd/ssl/bootstrap-token.csv
$ 05c645cec943aef73c8b1f54464120c0,kubelet-bootstrap,10001,"system:kubelet-bootstrap"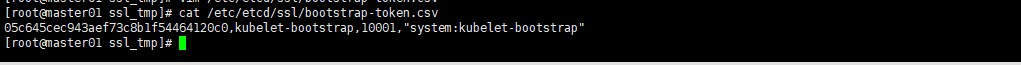
- 创建基础用户名/密码认证配置(密码、用户名、uid为后面创建dashborad后用户认证)
$ vim /etc/etcd/ssl/basic-auth.csv
$ admin,admin,1
readonly,readonly,2
- 部署Kubernetes API Server
$ cat > /usr/lib/systemd/system/kube-apiserver.service <<EOF
[Unit]
Description=Kubernetes API Server
Documentation=https://github.com/GoogleCloudPlatform/kubernetes
After=network.target
[Service]
ExecStart=/usr/local/bin/kube-apiserver \
--admission-control=NamespaceLifecycle,LimitRanger,ServiceAccount,DefaultStorageClass,ResourceQuota,NodeRestriction \
--bind-address=192.168.184.28 \
--insecure-bind-address=127.0.0.1 \
--authorization-mode=Node,RBAC \
--runtime-config=rbac.authorization.k8s.io/v1 \
--kubelet-https=true \
--anonymous-auth=false \
--basic-auth-file=/etc/etcd/ssl/basic-auth.csv \
--enable-bootstrap-token-auth \
--token-auth-file=/etc/etcd/ssl/bootstrap-token.csv \
--service-cluster-ip-range=10.1.0.0/16 \
--service-node-port-range=20000-40000 \
--tls-cert-file=/etc/etcd/ssl/kubernetes.pem \
--tls-private-key-file=/etc/etcd/ssl/kubernetes-key.pem \
--client-ca-file=/etc/etcd/ssl/ca.pem \
--service-account-key-file=/etc/etcd/ssl/ca-key.pem \
--etcd-cafile=/etc/etcd/ssl/ca.pem \
--etcd-certfile=/etc/etcd/ssl/kubernetes.pem \
--etcd-keyfile=/etc/etcd/ssl/kubernetes-key.pem \
--etcd-servers=https://192.168.184.28:2379,https://192.168.184.29:2379,https://192.168.184.30:2379 \
--enable-swagger-ui=true \
--allow-privileged=true \
--audit-log-maxage=30 \
--audit-log-maxbackup=3 \
--audit-log-maxsize=100 \
--audit-log-path=/etc/etcd/log/api-audit.log \
--event-ttl=1h \
--v=2 \
--logtostderr=false \
--log-dir=/etc/etcd/log
Restart=on-failure
RestartSec=5
Type=notify
LimitNOFILE=65536
[Install]
WantedBy=multi-user.target
EOF- 启动
$ systemctl daemon-reload
$ systemctl enable kube-apiserver.service && systemctl start kube-apiserver.service
$ systemctl status kube-apiserver.service- 部署Controller Manager服务
$ cat > /usr/lib/systemd/system/kube-controller-manager.service <<EOF
[Unit]
Description=Kubernetes Controller Manager
Documentation=https://github.com/GoogleCloudPlatform/kubernetes
[Service]
ExecStart=/usr/local/bin/kube-controller-manager \
--address=127.0.0.1 \
--master=http://127.0.0.1:8080 \
--allocate-node-cidrs=true \
--service-cluster-ip-range=10.1.0.0/16 \
--cluster-cidr=10.2.0.0/16 \
--cluster-name=kubernetes \
--cluster-signing-cert-file=/etc/etcd/ssl/ca.pem \
--cluster-signing-key-file=/etc/etcd/ssl/ca-key.pem \
--service-account-private-key-file=/etc/etcd/ssl/ca-key.pem \
--root-ca-file=/etc/etcd/ssl/ca.pem \
--leader-elect=true \
--v=2 \
--logtostderr=false \
--log-dir=/o/etc/etcd/log
Restart=on-failure
RestartSec=5
[Install]
WantedBy=multi-user.target
EOF- 启动
$ systemctl daemon-reload
$ systemctl enable kube-controller-manager.service && systemctl start kube-controller-manager.service
$ systemctl status kube-apiserver.service- 部署Kubernetes Scheduler:
$ cat > /usr/lib/systemd/system/kube-scheduler.service <<EOF
[Unit]
Description=Kubernetes Scheduler
Documentation=https://github.com/GoogleCloudPlatform/kubernetes
[Service]
ExecStart=/usr/local/bin/kube-scheduler \
--address=127.0.0.1 \
--master=http://127.0.0.1:8080 \
--leader-elect=true \
--v=2 \
--logtostderr=false \
--log-dir=/etc/etcd/log
Restart=on-failure
RestartSec=5
[Install]
WantedBy=multi-user.target
EOF $ systemctl daemon-reload
$ systemctl enable kube-scheduler.service && systemctl start kube-scheduler.service
$ systemctl status kube-scheduler.service
$ netstat -nlpt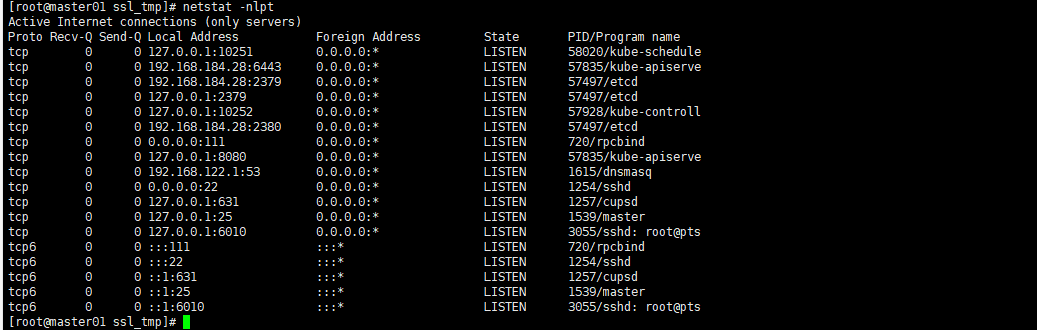
3、部署kubectl 命令行工具
- 准备二进制命令包
$ cd && export KUBE_URL="https://storage.googleapis.com/kubernetes-release/release/v1.8.2/bin/linux/amd64"
$ wget "${KUBE_URL}/kubelet" -O /usr/local/bin/kubelet
$ wget "${KUBE_URL}/kubectl" -O /usr/local/bin/kubectl
$ chmod +x /usr/local/bin/kubelet /usr/local/bin/kubectl
$ scp /usr/local/bin/kubelet 192.168.184.29:/usr/local/bin/kubelet
$ scp /usr/local/bin/kubectl 192.168.184.29:/usr/local/bin/kubectl
$ scp /usr/local/bin/kubelet 192.168.184.30:/usr/local/bin/kubelet
$ scp /usr/local/bin/kubectl 192.168.184.30:/usr/local/bin/kubectl
$ scp -r /usr/local/bin/cni/* 192.168.184.29:/usr/local/bin/cni/
$ scp -r /usr/local/bin/cni/* 192.168.184.30:/usr/local/bin/cni/- 创建 admin 证书签名请求
$ cd /etc/etcd/ssl_tmp
$ cat > admin-csr.json <<EOF
{
"CN": "admin",
"hosts": [],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"ST": "BeiJing",
"L": "BeiJing",
"O": "system:masters",
"OU": "System"
}
]
}
EOF- 生成 admin 证书和私钥:
$ cfssl gencert -ca=/etc/etcd/ssl/ca.pem -ca-key=/etc/etcd/ssl/ca-key.pem -config=/etc/etcd/ssl/ca-config.json -profile=kubernetes admin-csr.json | cfssljson -bare admin
$ cp admin*.pem /etc/etcd/ssl/- 设置集群参数
$ kubectl config set-cluster kubernetes --certificate-authority=/etc/etcd/ssl/ca.pem --embed-certs=true --server=https://192.168.184.28:6443 - 设置客户端认证参数
$ kubectl config set-credentials admin --client-certificate=/etc/etcd/ssl/admin.pem --embed-certs=true --client-key=/etc/etcd/ssl/admin-key.pem- 设置上下文参数
$ kubectl config set-context kubernetes --cluster=kubernetes --user=admin- 设置默认上下文
$ kubectl config use-context kubernetes- 使用kubectl工具
$ kubectl get cs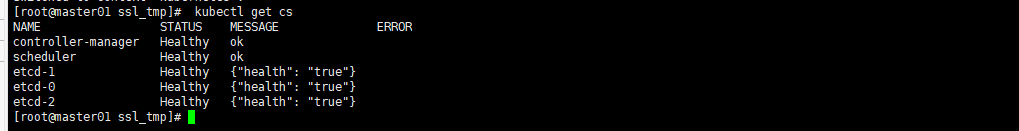
- 验证master节点功能:
$ kubectl get componentstatuses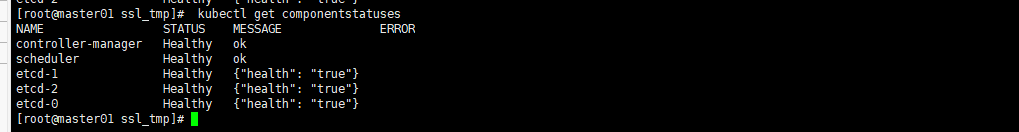
本作品采用《CC 协议》,转载必须注明作者和本文链接





 关于 LearnKu
关于 LearnKu


推荐文章: